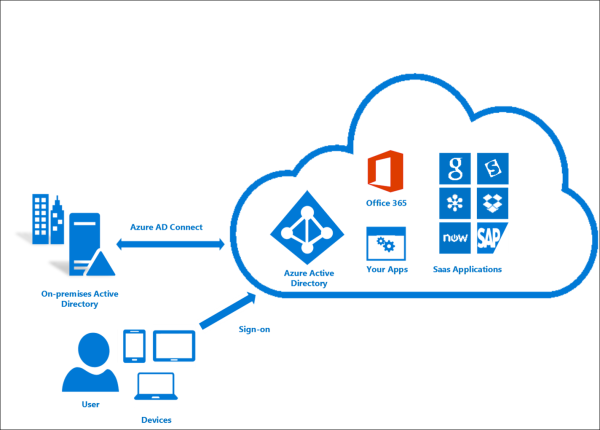
Want to integrate your on-prem Active Directory with Azure? Azure AD Connect makes this simple. Azure AD Connect is the answer (for now!) The techniques for doing this have changed many times over the years – this document provides the options and comparisons for you:
AD to Azure Integration Options
This connectivity provides the following:
- Users can use a single identity to access on-premises applications and cloud services such as Office 365
- Single tool to provide an easy deployment experience for synchronization and sign-in
- Provides the newest capabilities for your scenarios; Azure AD Connect replaces older versions of identity integration tools such as DirSync and Azure AD Sync; see the link above
Azure AD Connect consists of the following three components:
- Synchronization – this component is responsible for creating users, groups, and other objects; it is also responsible for making sure identity information for your on-premises users and groups is matching the cloud
- AD FS – federation is an optional part of Azure AD Connect and can be used to configure a hybrid environment using an on-premises AD FS infrastructure; this can be used by organizations to address complex deployments, such as domain join SSO, enforcement of AD sign-in policy, and smart card or 3rd party MFA
- Health Monitoring – Azure AD Connect Health can provide robust monitoring and provide a central location in the Azure portal to view this activity
Before installing this feature, you need to go through these hardware and software requirements carefully in order to ensure success. Note that there is an Express Setup option and this is only going to work if you have met all of these prerequisites. Note also that AD Federation Services in your on-prem is not necessarily a requirement.
Finally, here is a link to the Express Settings step-by-step: